Table of Contents
Description
This guide will walk through the proces of creating a security Group combined with a PIM enabled group that will give members eligility to elevate and become User Administrator (any other role could apply, I just this admin role for this demo).
The issue
If we were to grant users direct eligible assignment to an Entra Administrative role, e.g. “User Administrator”, it would look like this on the role:
And visible on the “Assigned Roles” tab on the user object in Entra ID:
BUT if we wanted to control admin roles with groups, how should be approach this?
We could create a PIM enabled group, that was had active assignment to the “User Administrator” role: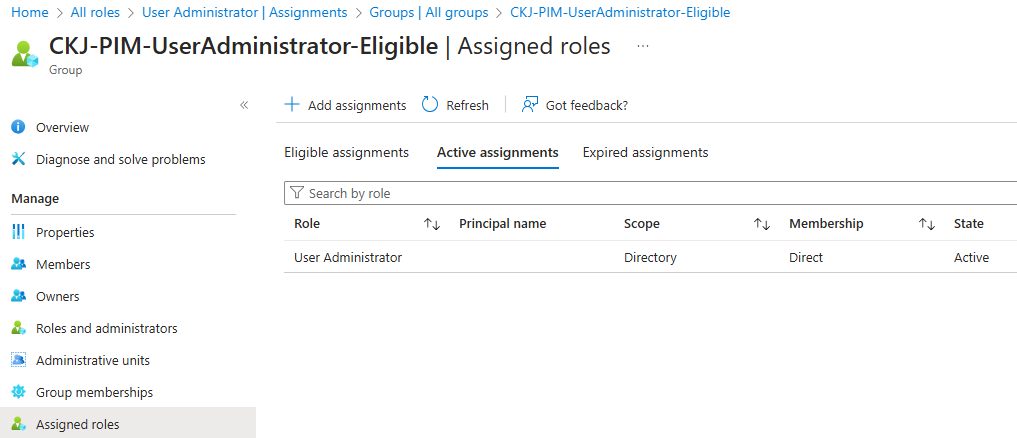
And added my user as eligible member of the security group: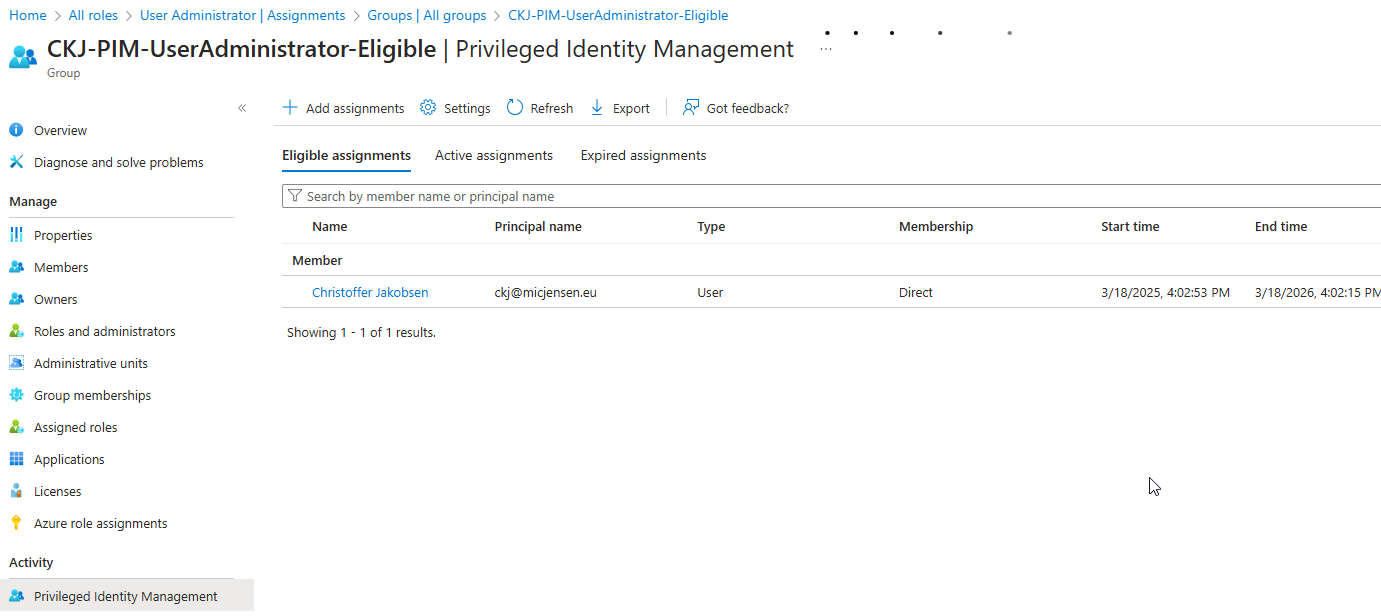
This however would mean that I lost visibility over the added permission directly on the user:
And since my user is only eligible member on the security group, the membership of the security group is not visible either:
We could choose to educate our support staff to use PIM administration in Azure (and we should for sure). This would give us overview over PIM enabled groups: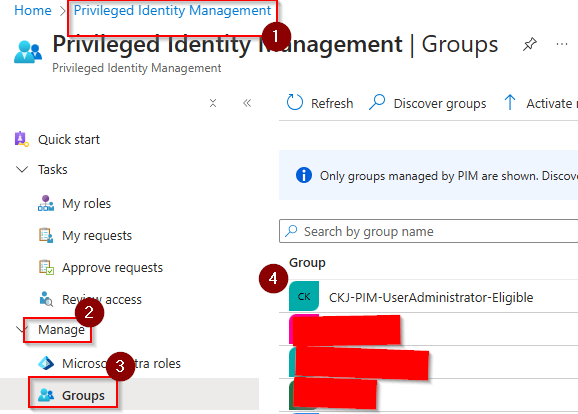
And eligible members of the groups:
But not directly what admin roles were assigned to the group. You would have to use proper naming convention,take note of that group name and then go to Entra Roles within PIM:
And look for active assignments where the group would be present.
But can we use security groups and still make it more visible on the user itself? I would say so, and the next section is about how to configure this.
The solution
Solution drawing
Naming Convention
Take some time to work with naming convention. For this demo, the naming convention is very basic, but the goal should be to get an understanding on the user object that the user is member of a group that grants administrative role via PIM.
One could say that the standard security group that members should be active assigned to, should be called something with “eligible” to make it even more visible on the user object, that the group that the user is member of, is not a permanent active membership, but only eligible and must be used with PIM. Others might say that if the company have strict PIM implementation, it would not be needed since they always would configure eligible.
Create groups
Create Security Group – PIM enabled – Entra Roles
Start by creating a group – this group must be enabled for Entra Roles.
Add the “User Administrator” role to the group:
I can be a good idea to check afterwards that the security group got active membership on the admin role. If for some reason the membership on the admin role is eligible, that would create a scenario where a user whould have to first PIM for the security group and then again for the admin role.
Go into the newly created group and enable PIM:
Create Security Group for members
Create a standard Security Group and add the user as member:
Join standard security group to PIM enabled security group
Now go back to the PIM enabled group we created first, and then add the second standard security group as eligible member of this PIM enabled security group:
Validate
I can now see that my user have membership over a group with a naming convention that enables me to understand that the user have and User Administrator role via PIM:
And if I go to PIM as my user, I can now see the group that I should activate to get the “User Administrator” role:

Comments